Nobody in my town can connect to the municipal WiFi. It broadcasts, your phone sees it, you tap it — and nothing happens. This has been going on for months. The kind of broken that local government excels at: visibly present, functionally absent. I work around town and I see it every time.
This isn’t security work. It’s recon for a conversation I’m planning to have with the council.
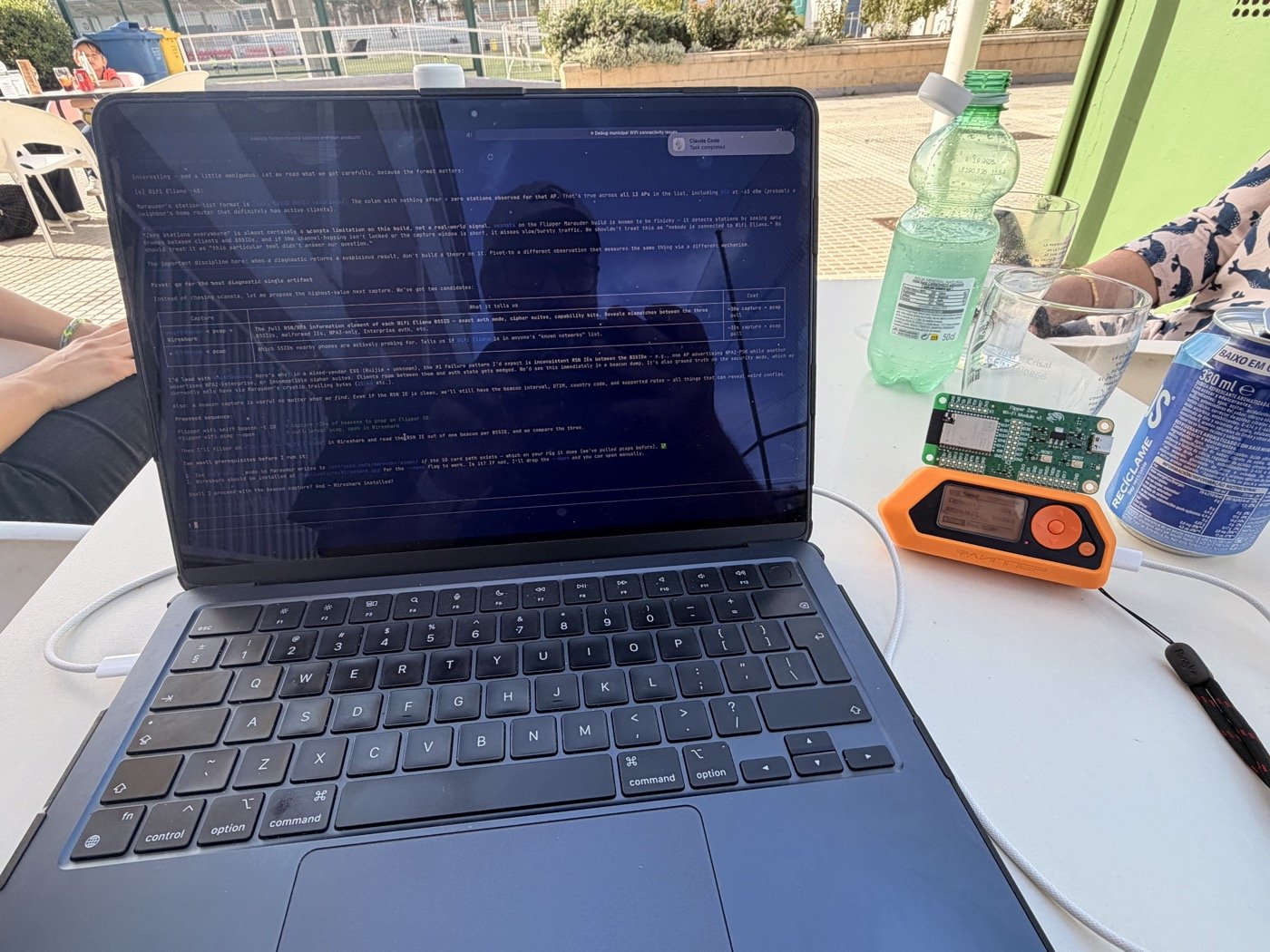
So I pointed a Flipper Zero with a WiFi dev board at it and ran Marauder’s scanap command. Three BSSIDs came back broadcasting “the municipal network” — two on channel 6, one on channel 11, two different vendors. Strongest signal at -48 dBm, which is solid. The network exists. The hardware is real.
Each line of Marauder’s output had two trailing hex bytes after the network name and signal strength. The tool doesn’t document them — no mention in the wiki, no label in the output.
My guess: the 802.11 Capability Information field — two bytes every AP broadcasts in its beacons. It’s a bitfield, and bit 4 — the Privacy bit — tells you whether the network requires encryption.
All three the municipal network BSSIDs showed 0x0421. I unpacked the bits:
0x0421 = 0000 0100 0010 0001
^
bit 4 = 0 → Privacy clear → open networkEncrypted networks in the same scan showed 0x0431, 0x1431, 0x1511 — all with bit 4 set. The municipal network is genuinely open. No WPA, no WPA2, no hidden auth. That ruled out every encryption-related failure mode in one pass.
Next I ran sniffraw on channel 11. Ten beacons, 63 management frames, 52 probe responses — and zero data frames, zero EAPOL handshakes, zero deauth attacks. The APs are broadcasting, responding to probes, and then nothing. No client ever completes a session.
That narrows it hard. Signal is strong, network is open, nobody’s jamming it. What’s left is layer 3 — and a dead captive portal is the prime suspect, because Spanish municipal WiFi loves captive portals the way Spanish bureaucracy loves stamps. Dead DHCP or a broken backhaul are the other candidates.
One firmware gotcha: Marauder’s _flipper.bin UART bridge doesn’t write pcap files from sniffraw. My SD card file was 24 bytes — just the header, zero packets. You need the companion .fap app. I burned fifteen minutes on that before I thought to check the file size.
The scanap output already contained enough to rule out six failure modes. I didn’t need more scans — I needed to understand two bytes the tool gave me but didn’t explain. Most debugging tools are like this: they output more than they document, and the answer is often in data you already captured, in the fields you scrolled past because nobody labelled them.
A two-minute laptop test will close the case, but that’s just confirmation. The interesting part was already in the hex.
